Provisioning Zero Trust Access
Introduction
Privileged Access Management (PAM) systems solve a fundamental enterprise security problem: how to provide privileged access without distributing privileged credentials.
In a traditional environment, administrators often know the passwords, SSH keys, or secrets associated with shared administrative accounts. This creates significant operational and security challenges. Shared credentials eliminate accountability, complicate auditing, increase insider risk, and make it difficult to enforce least privilege access.
Modern PAM platforms address this challenge by mapping personal identities to shared privileged accounts. For example, a PAM solution may allow a member of a designated Entra ID administrative group to access the Administrator account on a domain controller without ever revealing the actual credentials. The PAM platform brokers the session, injects vaulted credentials, and records which individual accessed the system and when.
This model provides personal accountability for privileged actions while enabling centralized governance, auditing, and policy enforcement.
To achieve this, PAM platforms commonly use techniques such as:
- Session gateways and traffic proxies
- Credential injection
- Temporary credential provisioning
- Automatic password or key rotation
- Network path enforcement
- Endpoint isolation and traffic restrictions
- Session recording and command monitoring
While these enforcement methods vary across vendors and architectures, the core challenge remains the same:
How to provision privileged access securely while supporting real-world operational requirements?
This article explores several Zero Trust privileged access provisioning models that organizations commonly implement to balance security, operational efficiency, and user experience.
Core Access Provisioning Requirements
Most enterprise privileged access scenarios are built from a combination of several foundational access models.
These models include:
- Role-based access to shared privileged accounts
- Common account access across multiple endpoints
- Endpoint-based access
- Just-in-time access
- Access requests with business justification
- Dual control access
- Human or AI-assisted approval workflows
- Network-Based Access Provisioning
- Isolated Administrative Environments
In practice, organizations rarely implement only one model. Instead, multiple provisioning methods are layered together to achieve the desired level of control and operational flexibility.
For example:
-
A highly sensitive administrator account may require RBAC assignment and approval workflow.
-
A production emergency access workflow may require override access combined with dual control access provisioning.
-
A Zero Trust administrative environment may combine ESAE access with just-in-time provisioning.
The remainder of this article examines each provisioning model individually.
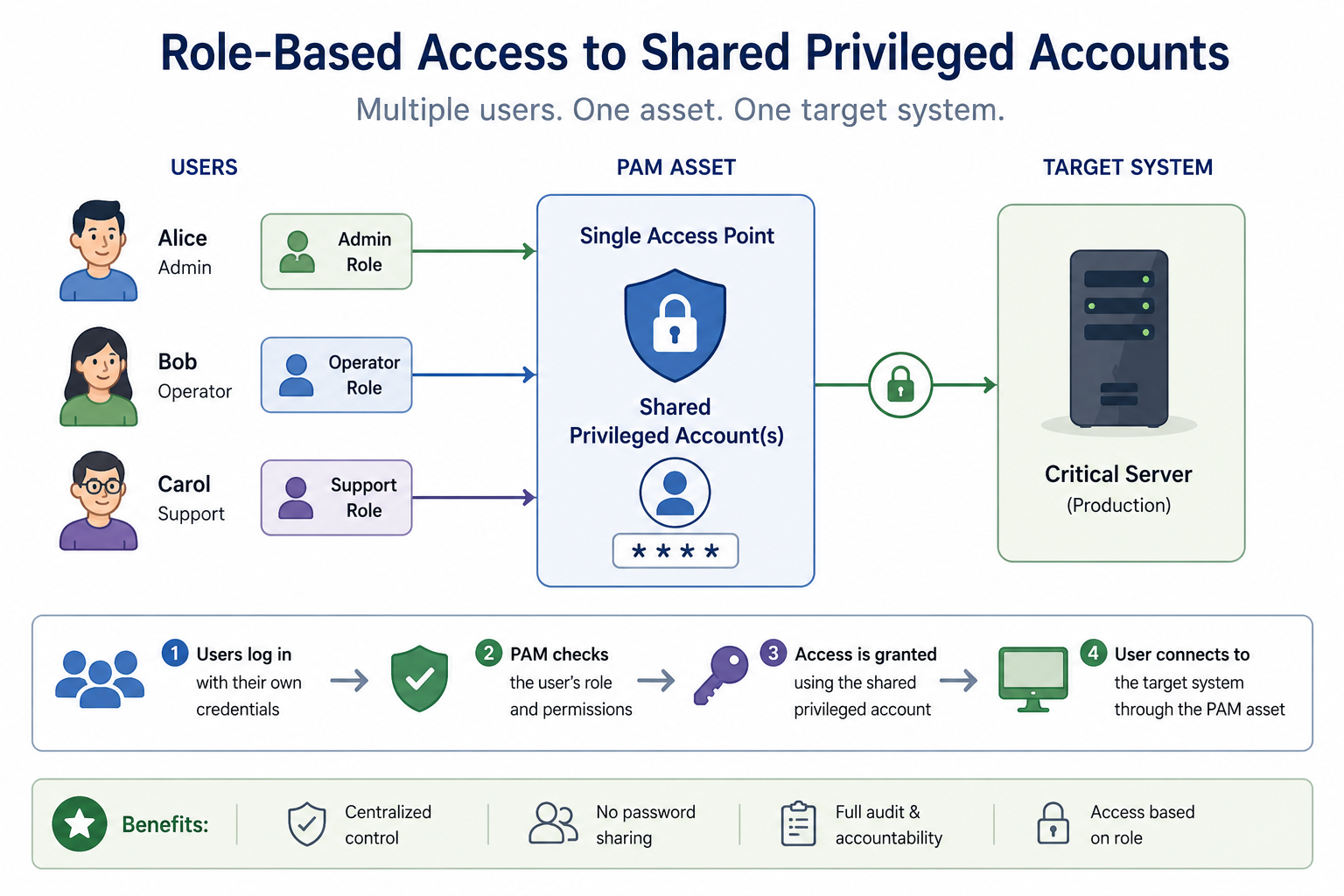
Role-Based Access to Shared Privileged Accounts
The most common privileged access provisioning model is Role-Based Access Control (RBAC).
In this model, users are granted permissions to access a PAM-managed asset without being able to view or retrieve the underlying credentials. Instead of distributing passwords, SSH keys, or secrets to administrators, the PAM server brokers the connection and launches the session on behalf of the user while keeping the credentials locked inside the secure vault.
12Port PAM allows to assign access permissions directly to individual users or provisioned through identity groups and security roles. These roles are typically synchronized from enterprise identity providers such as:
- Microsoft Active Directory
- LDAP directories
- Microsoft Entra ID
Using centralized identity groups simplifies administration and enables organizations to align privileged access with existing enterprise RBAC policies.
In addition to integrated directory groups, 12Port PAM also supports locally managed groups. These local groups may contain:
- Local PAM users
- Active Directory users
- LDAP users
- Entra ID users
- Nested PAM groups
This hybrid group management model provides additional flexibility for organizations that require PAM-specific authorization structures independent from enterprise directory administration.
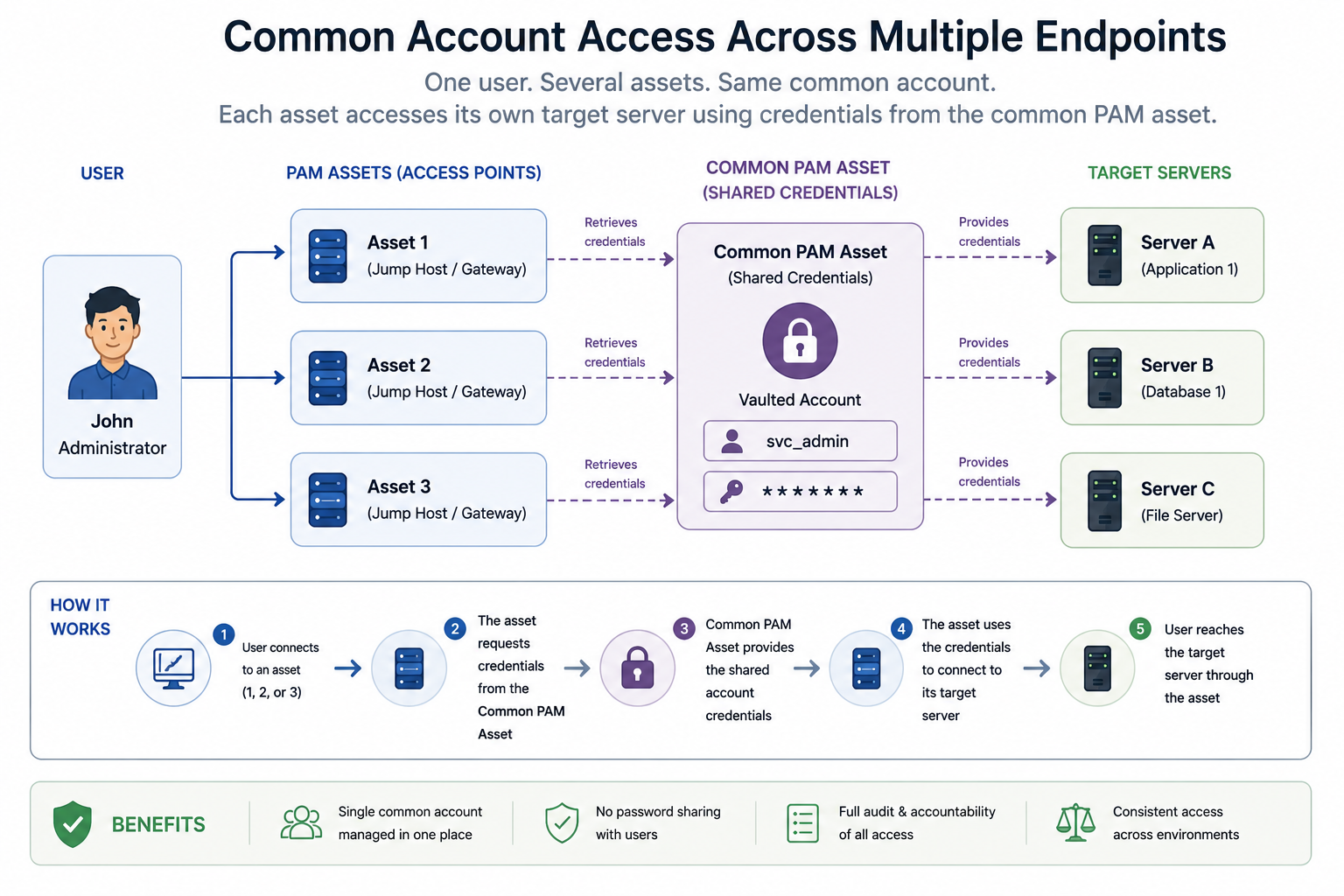
Common account access across multiple endpoints
In many enterprise environments, the same privileged account is reused across multiple systems and services.
Common examples include:
- Domain administrator accounts
- Service accounts distributed through Microsoft Active Directory
- Privileged application identities
- Automation and orchestration accounts
12Port PAM provides two flexible mechanisms for provisioning access to reused shared accounts:
- Member Assets
- Referenced Assets
Member Assets
The Member Asset model allows system owners to associate a shared privileged account directly with multiple endpoint assets.
In this approach, the privileged account itself is managed independently from the endpoints that use it. Users accessing a target endpoint can select the associated privileged member asset as part of the connection workflow.
Referenced Assets
The Referenced Asset model allows system owners to reuse a centrally managed privileged asset within an endpoint asset while overriding or extending selected characteristics of the original asset. In this model, the referenced asset typically represents the shared privileged account or credential, while the referencing asset defines the target host, application, or execution context associated with that credential. Alternatively, the referenced asset might provide connection or application properties while the referencing assets can enhance it with specific credentials.
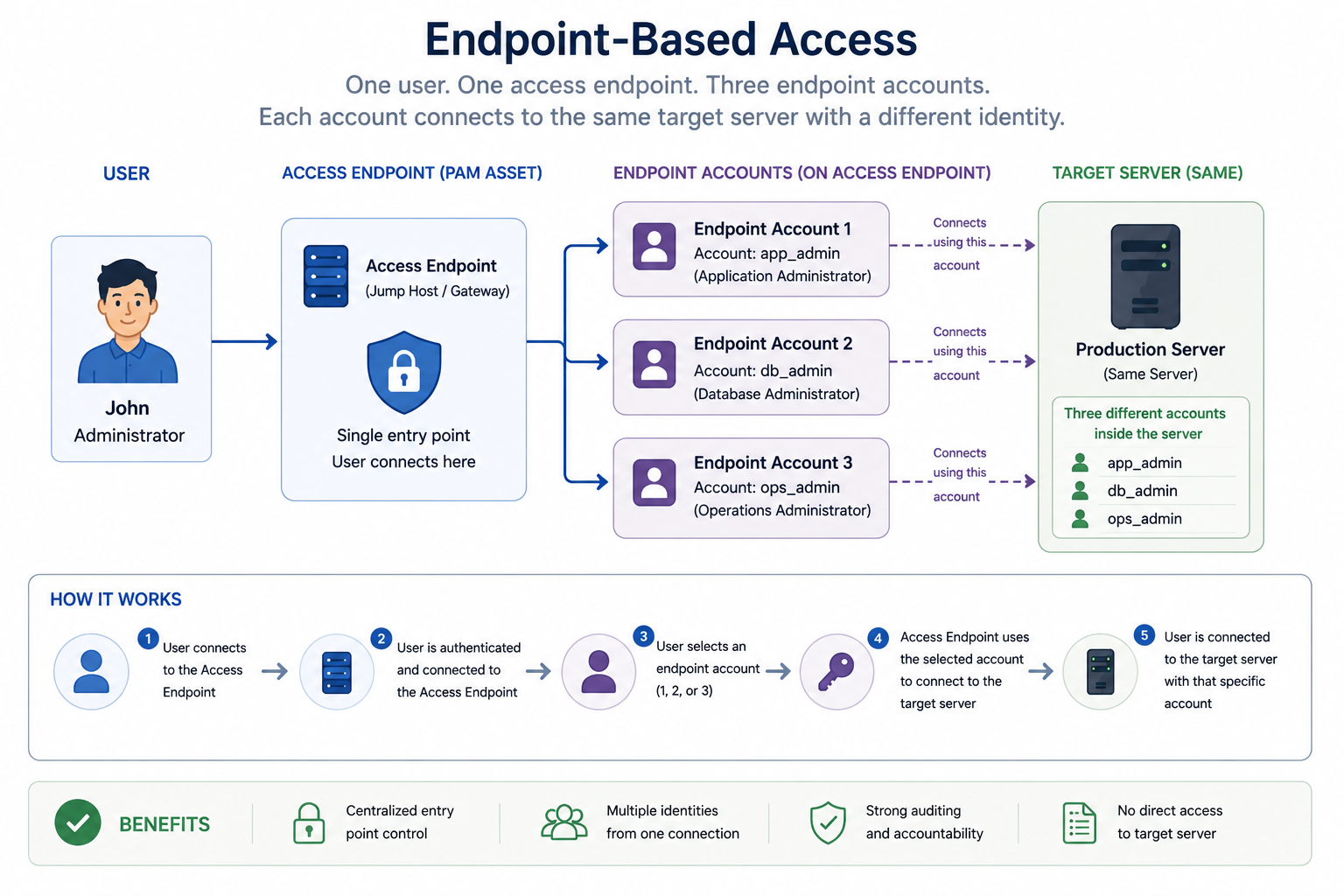
Endpoint-based access
Traditional PAM architectures generally aim to minimize the number of privileged accounts configured on a single endpoint. Reducing the number of administrative identities simplifies credential management, limits attack surface, and improves overall security posture.
In practice, however, many enterprise systems require multiple privileged access paths to support operational and administrative requirements.
For example, a single endpoint may:
- Host multiple workloads managed by different service owners
- Require separate accounts with different privilege levels
- Support operational separation between infrastructure, application, and database teams
- Use platform-specific privilege escalation workflows such as Cisco enable levels
- Require different administrative contexts for automation, maintenance, and troubleshooting
12Port PAM supports an endpoint-based access model where multiple privileged account assets can be associated with a primary host asset.
In this architecture:
- The primary asset represents the endpoint or host
- Member assets represent individual privileged accounts, applications, or privilege contexts available on that endpoint
When users launch a session, they simply select the member asset corresponding to the account or privilege level required for their task.
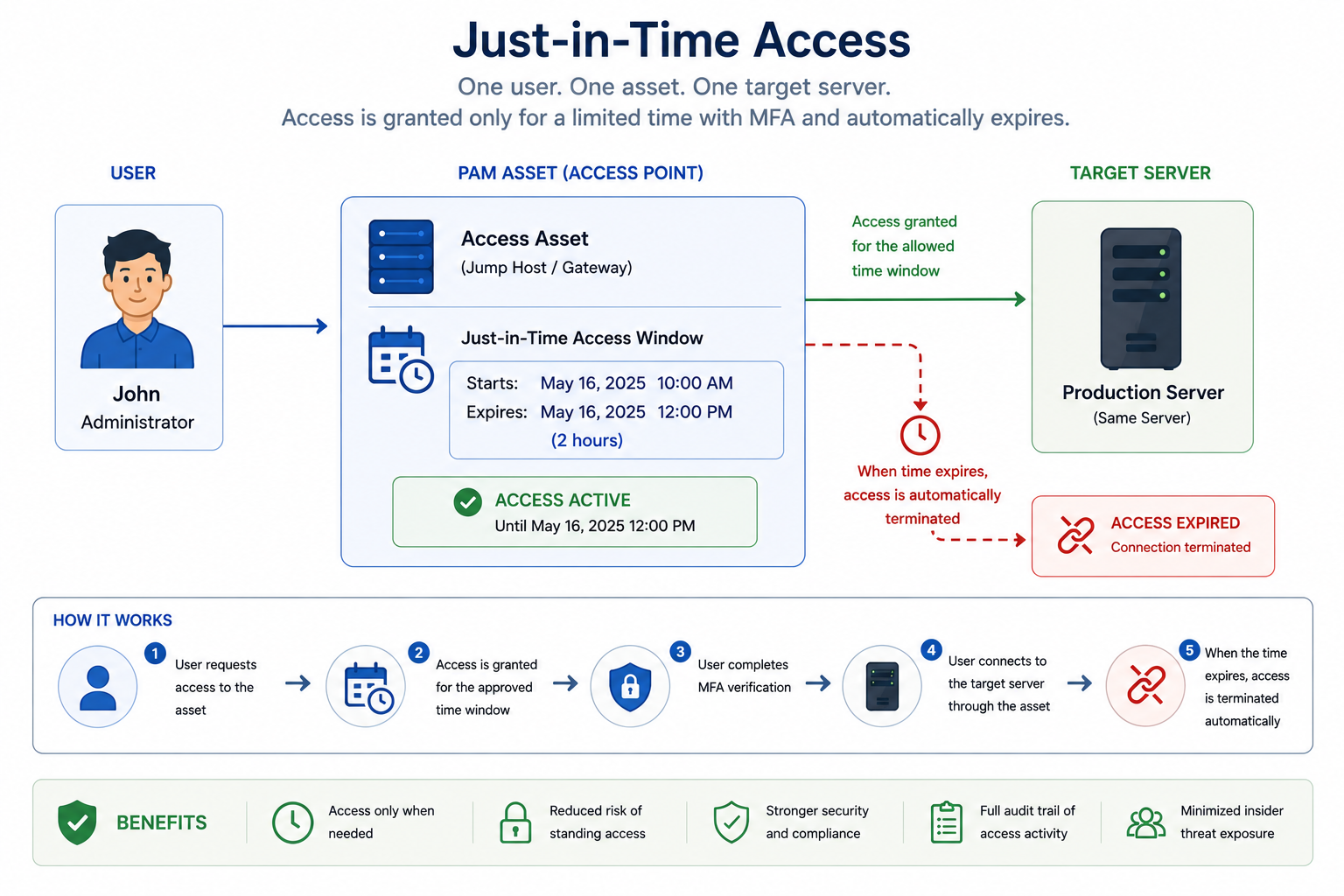
Just-in-time access
One of the key principles of Zero Trust security is eliminating standing privileged access. Even users who are authorized to access sensitive systems should not retain permanent privileges that can be abused, compromised, or misused outside approved operational windows.
To support this model, 12Port PAM provides a just-in-time (JIT) access provisioning mechanism that allows privileged users to request temporary access to sensitive resources for a specific time and duration.
Instead of maintaining always-on administrative privileges, access is dynamically provisioned only when required and only under the conditions defined by organizational security policies.
System owners can define additional controls around the access request process, including:
- Restricting access from specific network locations
- Requiring MFA verification at the time of access
- Limiting access to approved maintenance windows
- Validating requested duration against policy limits
- Enforcing contextual or risk-based access conditions
Once submitted, access requests can be approved through:
- Human approval workflows
- Administrative dual-control procedures
- AI-driven policy evaluation and approval engines
After approval, 12Port PAM provisions the requested access only for the approved period of time. During that access window, the platform continuously enforces security policies governing:
- Access initiation
- Session suspension
- Automatic termination
- Time expiration
- Policy violations
Access requests with business justification
In some environments, granting privileged access is not only a technical decision but also an operational and compliance requirement. Organizations often require users requesting privileged access to provide a business justification explaining why the access is needed.
These justifications serve several important purposes:
- Supporting security investigations
- Improving audit and compliance reporting
- Correlating privileged activity with operational tasks
- Enforcing administrative accountability
- Educating users about responsible privileged access usage
For these scenarios, 12Port PAM supports automatically approved access requests that still require users to provide a reason for the requested access.
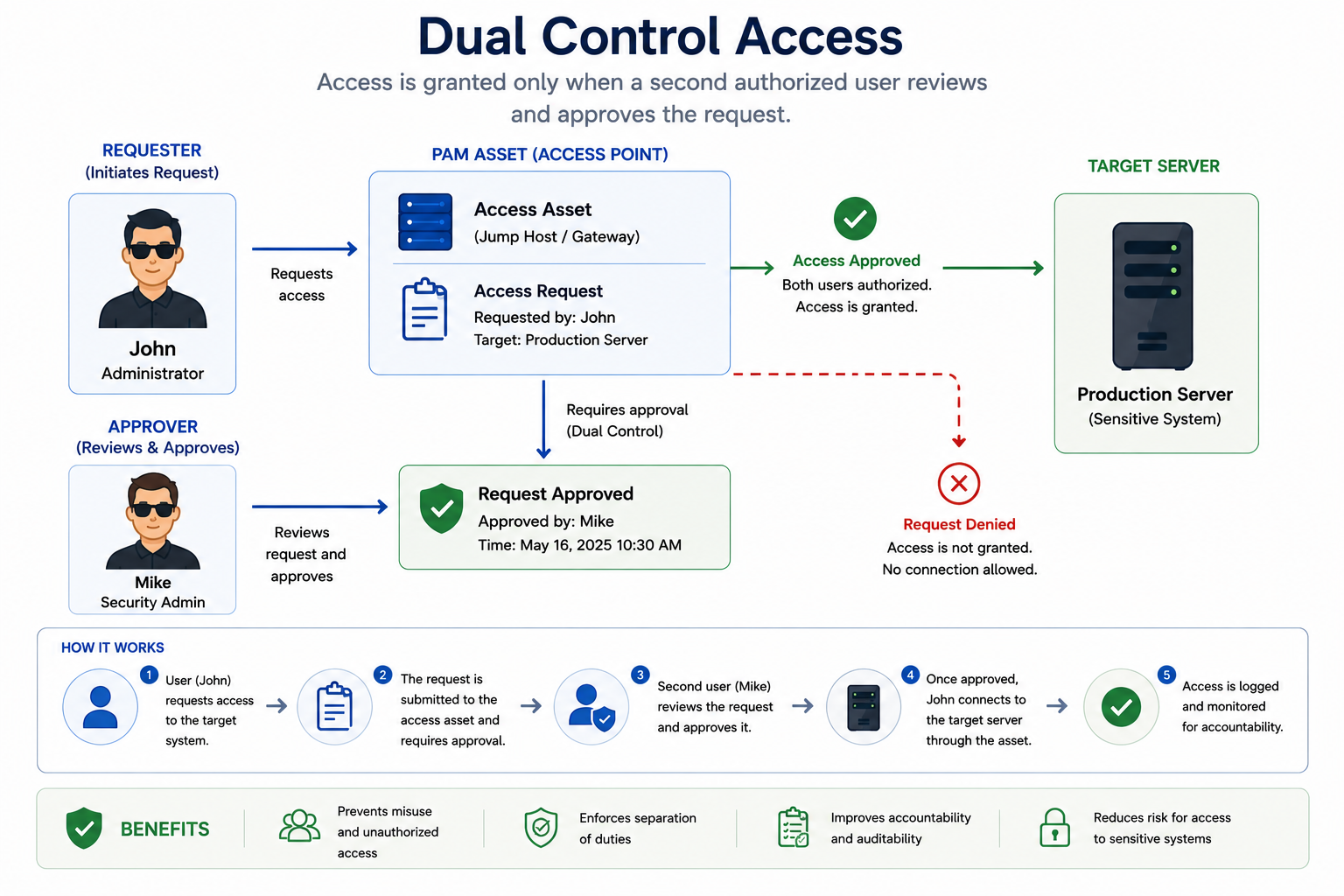
Dual control access
Controlling privileged access for IT administrators is one of the most difficult challenges in enterprise security. Administrators build and maintain infrastructure, manage security systems, support users, and often possess broad access across the environment. Even when direct endpoint access is restricted, administrators may still control the PAM platform responsible for provisioning that access.
Because of this, highly sensitive environments often require additional safeguards beyond standard RBAC and just-in-time provisioning.
One common approach is implementing administrative dual control, where two authorized administrators participate in the access provisioning process. In this model, one administrator requests privileged access while another independently approves the request before access is granted.
This separation of duties helps organizations:
- Reduce insider risk
- Prevent unauthorized privileged activity
- Enforce operational accountability
- Introduce peer oversight for sensitive actions
- Improve audit and compliance posture
Dual-control workflows are especially important when managing:
- Domain controllers
- Critical infrastructure
- Financial systems
- Government or defense environments
- Highly sensitive production systems
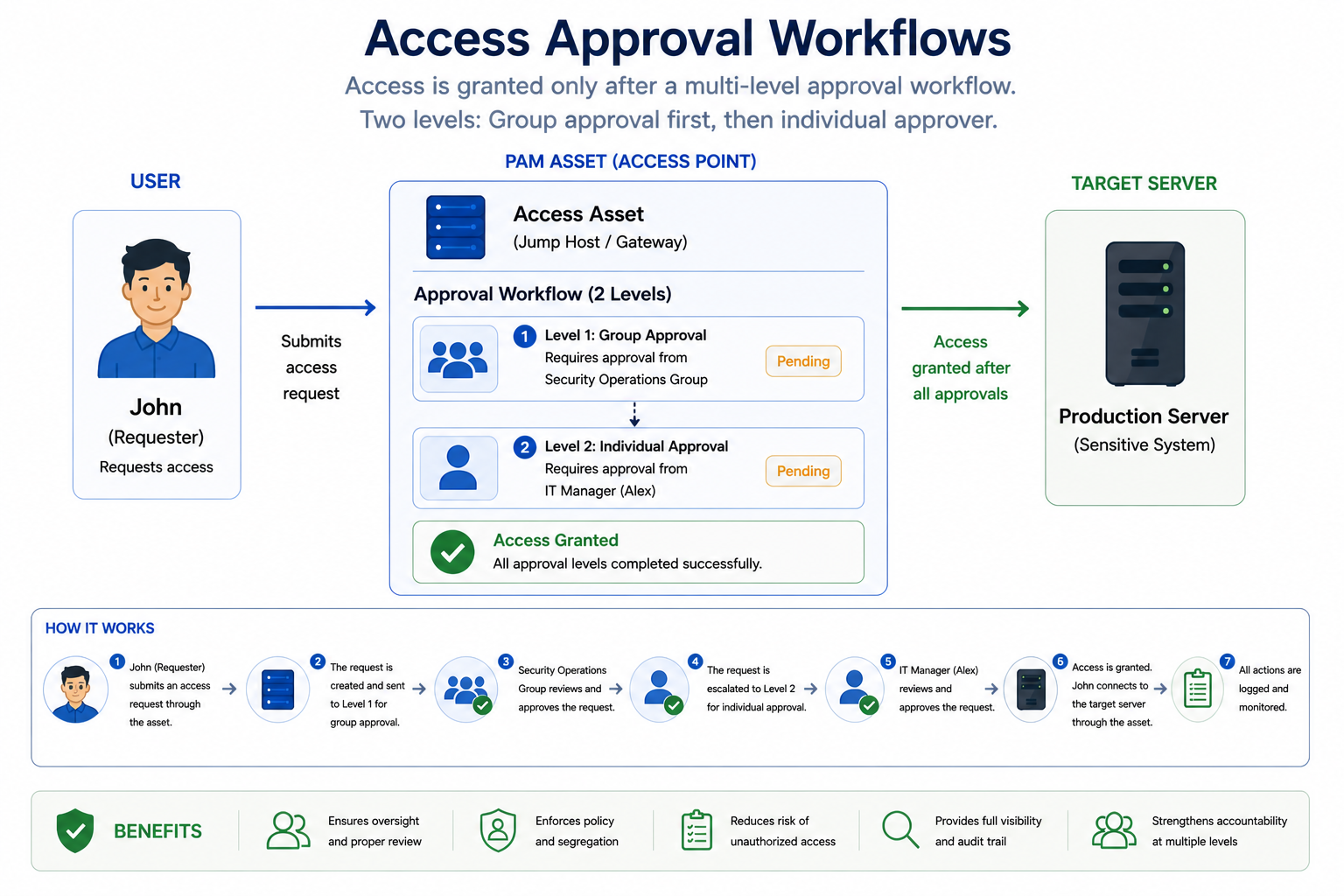
Access Approval Workflows
In many environments, privileged access should only be provisioned after a formal approval process. While role-based permissions and just-in-time access reduce standing privileges, organizations often require an additional layer of validation before granting access to sensitive systems or data.
This is especially important in scenarios involving shared operational responsibilities, external service providers, or highly regulated environments.
Common examples include:
- Administrators operating within large organizations with layered IT responsibilities
- Managed Service Providers (MSPs) accessing customer environments
- Equipment or software vendors maintaining systems inside corporate networks
- Help desk personnel accessing managed services and user systems
Once approved, the PAM platform dynamically provisions access according to the approved scope, duration, and policy restrictions.
12Port PAM provides flexible approval workflows designed to support both operational efficiency and strict governance requirements in complex enterprise environments.
Approval processes can be structured using multiple approval layers, where each stage must be approved before the request progresses to the next level. This allows organizations to implement hierarchical approval chains that align with administrative, security, or compliance responsibilities.
In addition to sequential approval stages, workflow levels can also support alternative approvers. Instead of requiring approval from a specific individual, organizations can define groups of approvers and specify how many members of that group must approve the request before the workflow can continue. This model improves flexibility and prevents operational delays caused by approver availability.
Approval workflows in 12Port PAM can involve both:
- Human approvers
- AI Agents performing automated policy evaluation and decision making
This hybrid approval model enables organizations to automate low-risk access decisions while still enforcing human oversight for sensitive operations.
To improve accountability and auditability, approvers are required to provide a reason when rejecting access requests and may optionally provide justification when approving them. These approval comments become part of the permanent audit trail and can later be correlated with access requests, session activity, security events, and compliance reporting.
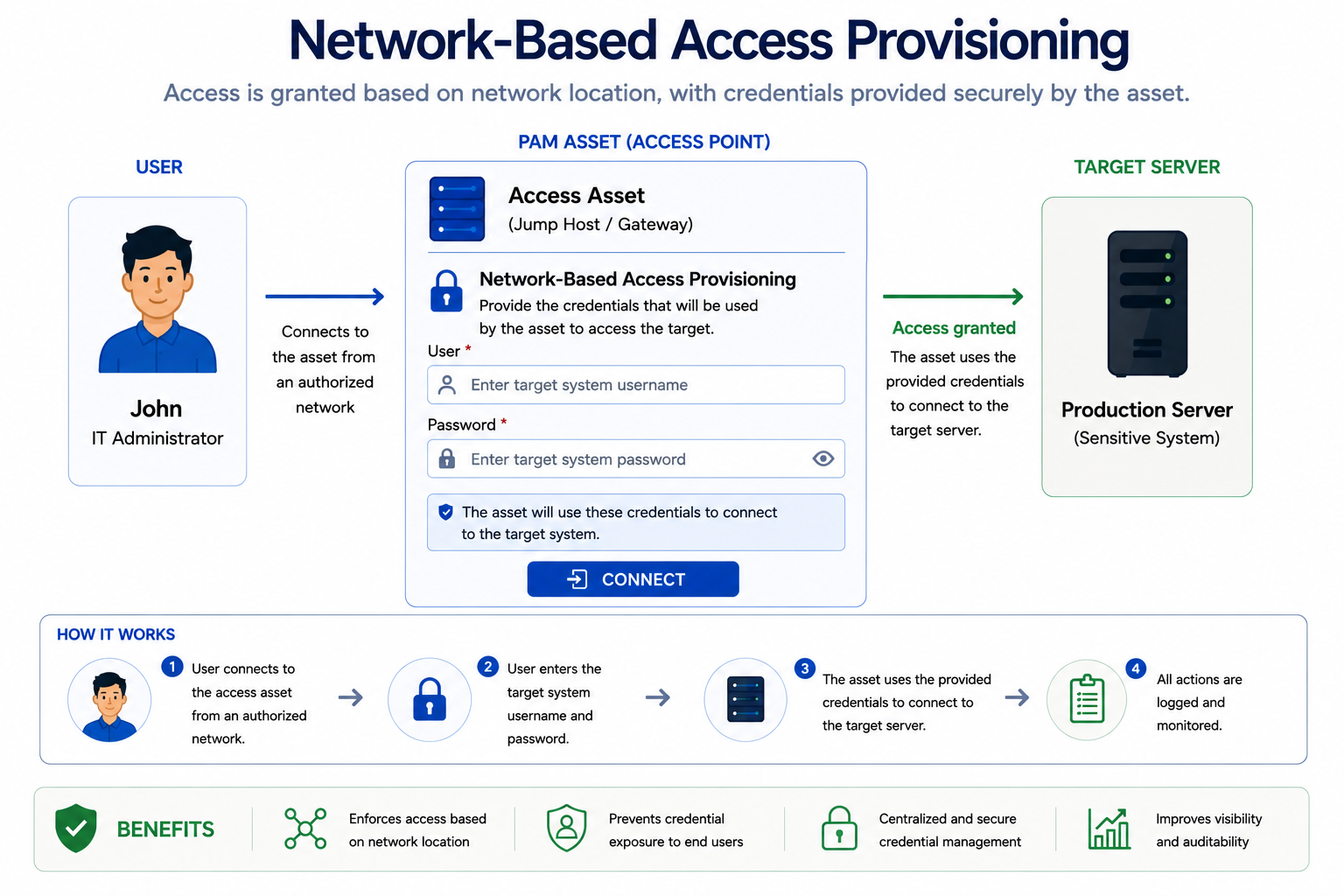
Network-Based Access Provisioning
Not all privileged access scenarios are based on shared privileged identities or vaulted credentials. In many environments, users already have their own authorized accounts on the destination systems, but network-level restrictions prevent them from connecting directly to those resources.
In these cases, access control is enforced primarily through network location and connectivity policies rather than through privileged credential provisioning.
Common examples include:
- Accessing corporate resources from outside the network perimeter
- Accessing cloud or on-premises systems that are reachable only through approved jump hosts
- Accessing endpoints protected by restrictive firewall rules
- Administrative access limited to specific management networks
- Segmented environments that block direct lateral connectivity
In these scenarios, users typically authenticate using their own personal credentials or other credentials already known to them rather than using vaulted privileged accounts provisioned by the PAM platform.
For these scenarios, system owners provision access through PAM assets that either utilize the user’s existing PAM authentication session or allow users to provide their own credentials at the time of connection.
Instead of provisioning a vaulted privileged identity, the asset acts as a transparent jump-host gateway that securely brokers the network connection to the destination resource.
In this model, users continue to authenticate with personal or otherwise known credentials, while the PAM platform enforces the network path, access policies, and session controls required to reach protected systems. This allows organizations to secure administrative connectivity without relying exclusively on identity-based privileged account protection.
Network-Based Access Provisioning is commonly combined with additional security controls such as:
- Role-Based Access Control (RBAC)
- Just-in-Time (JIT) access provisioning
- Access request and approval workflows
- MFA enforcement
- Session monitoring and auditing
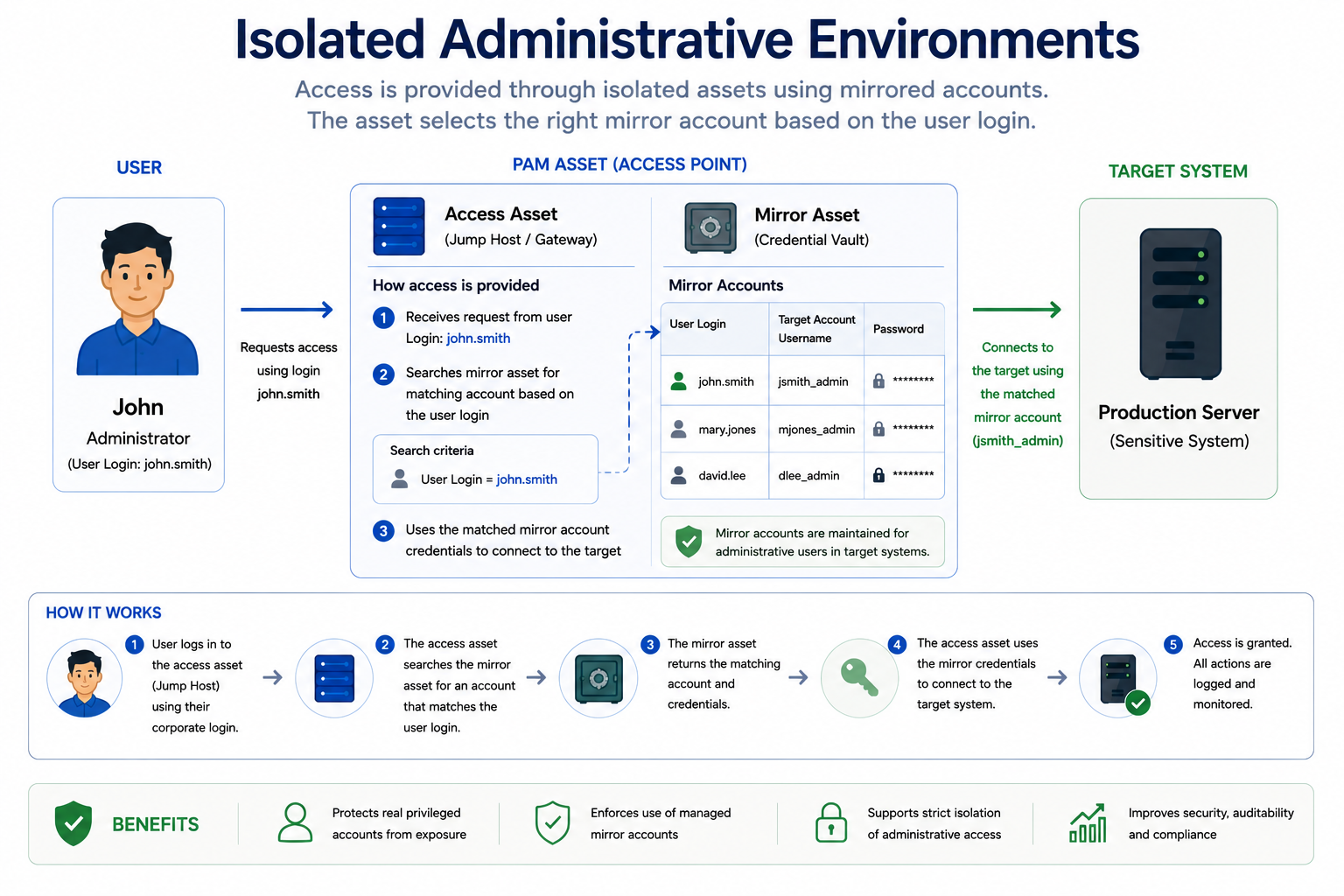
Isolated Administrative Environments
In highly sensitive and typically isolated security environments, users often operate with alternative identity accounts that are used exclusively to access protected resources. These dedicated administrative identities are intentionally separated from users’ everyday accounts and are only valid within the secured environment.
This additional layer of identity separation creates a strong security boundary between standard enterprise operations and highly privileged infrastructure. Even if a user’s regular workstation or corporate identity becomes compromised, attackers are prevented from directly accessing protected administrative environments.
This model is commonly used in environments where organizations must defend against advanced threats, lateral movement, credential theft, and supply-chain attacks.
Typical examples include:
- Microsoft Active Directory Red Forest implementations
- Enhanced Security Administrative Environments (ESAE)
- Disconnected or air-gapped networks
- Critical infrastructure management networks
- Sensitive government or defense environments
To support these types of isolated administrative environments, 12Port PAM provides a mechanism called Mirror Accounts. A mirror asset dynamically provisions access based on both the destination endpoint and the identity of the user requesting access. Instead of relying on a single shared privileged credential, the PAM platform resolves the appropriate alternative identity for the specific user and protected resource combination at the time of access.
This model allows organizations to implement highly granular identity separation policies within secured environments. Depending on organizational requirements, users may have:
- Individual alternative credentials for each protected asset
- Shared alternative administrative identities across multiple assets
- Dedicated administrative personas for isolated environments
- Environment-specific privileged identities separated from standard enterprise accounts
For example, a user may authenticate to the corporate environment using a standard identity while receiving a completely different administrative identity when accessing a protected ESAE or Red Forest resource.
To support this workflow, the 12Port PAM platform dynamically queries the credential vault during every access request using search criteria constructed from:
- The requesting user identity
- The destination asset
- Current RBAC permissions
- Applicable security policies
Summary
Modern PAM implementations must support far more than simple password vaulting. Different organizations, infrastructures, and threat models require different approaches to privileged access provisioning depending on operational, security, and compliance requirements.
This article explored several access provisioning models designed to support a wide range of network architectures, administrative practices, and Zero Trust security strategies. These models include RBAC-driven access, common account management, endpoint-based access, just-in-time provisioning, approval workflows, dual control, network-based access control, and isolated administrative environments.
While the number of possible scenarios (and the solutions) may initially appear overwhelming, most organizations typically implement only a subset of these models based on their specific operational and security needs. In practice, PAM deployments commonly combine multiple provisioning techniques to achieve the right balance between security, flexibility, accountability, and administrative efficiency.
As enterprise environments continue evolving toward hybrid infrastructure, segmented networks, and Zero Trust architectures, flexible privileged access provisioning becomes increasingly important. Modern PAM platforms must not only secure credentials, but also orchestrate how, when, where, and under what conditions privileged access is granted.