12 Port Node Architecture¶
Introduction¶
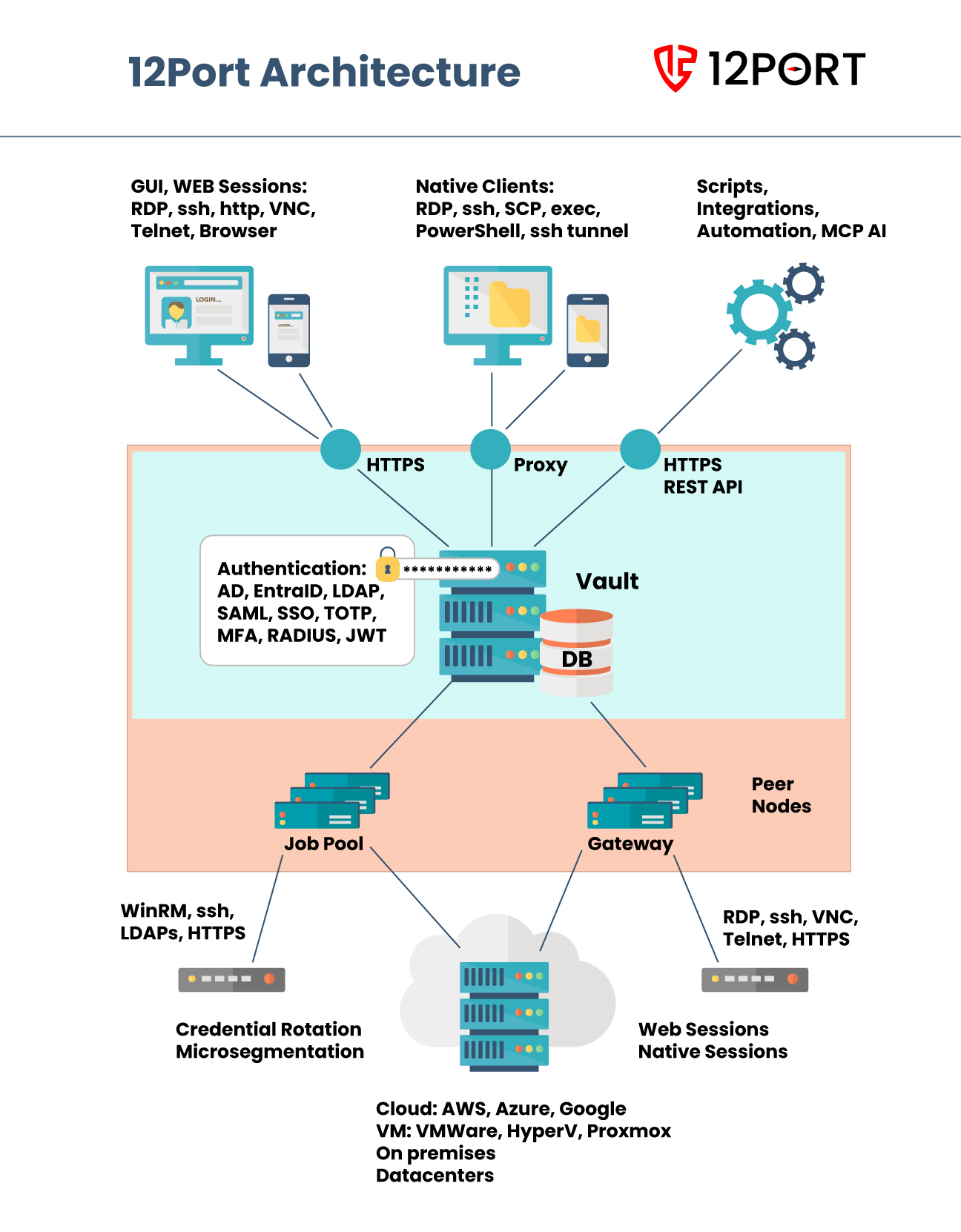
This article provides an overview of the components and data flows within a 12Port server node. It explains how clients, server components, and managed endpoints interact to deliver secure, centralized access and control.
Architecture¶
The diagram below illustrates the high-level components and data flows within the 12Port server architecture, including:
- The clients that access and interact with the server functionality
- The server components and how they communicate with each other
- The managed endpoints connected to the platform
Clients¶
-
WEB GUI. The Web GUI is a browser-based application that provides users with access to system configuration, management, auditing, reporting, and operational tasks. Users can browse assets, request access, and retrieve credentials from any desktop or mobile browser.
-
WEB Sessions. Web Sessions enable users to establish high-trust connections to remote endpoints directly from a browser. Supported protocols include RDP, SSH, HTTP, VNC, Telnet, and HTTP/RBI. Security is enforced through Role-Based Access Control (RBAC), approval workflows, multi-factor authentication (MFA), credential injection, as well as session recording and monitoring.
-
Third-Party Desktop and Mobile Clients. 12Port supports standard third-party clients that connect to endpoints through secure server-side proxies. These include tools using RDP, SSH, and PowerShell protocols, with full enforcement of RBAC, approval workflows, MFA, credential injection, and session recording.
Examples include Microsoft Remote Desktop (mstsc), PuTTY, WinSCP, PowerShell, MobaXTerm, and Unix-based terminals.
-
Automation, Integrations, and AI Agents. Scripts, third-party integrations, automation platforms, and AI agents can interact with the system via REST APIs, native protocols, or the MCP Server. These integrations support use cases such as configuration, management, auditing, reporting, and operational workflows like credential retrieval.
For example, an Ansible playbook can securely access endpoints using zero-trust SSH with credentials injected by 12Port, or an AI agent can discover and manage credentials for sensitive resources.
-
Inter-Node Communication. Multiple 12Port nodes communicate with each other via HTTP REST APIs to form a distributed architecture. This enables a unified control plane that provides centralized visibility, consistent security policies, and consolidated reporting, while allowing peer nodes to securely access endpoints across different environments.
Server Components¶
-
Secure Vault. The 12Port vault is built on either an embedded or external enterprise-grade database such as Oracle, Microsoft SQL Server, MySQL, or PostgreSQL. It securely stores configuration data, security policies, credentials, audit logs, and managed assets, ensuring controlled and auditable access.
-
Authentication Layer. The authentication layer integrates with enterprise identity systems, including Microsoft Active Directory, Entra ID, and LDAP directories. It also supports Single Sign-On (SSO) providers, multi-factor authentication (MFA) solutions such as TOTP, HOTP/RADIUS, YubiKey, and Duo Security, as well as API token-based authentication for programmatic access.
-
WEB Gateway. The Web Gateway enables secure, browser-based sessions to remote endpoints. It allows users to connect without installing local clients while maintaining full security controls and session visibility.
-
Job Engine (Job Pool). The Job Pool enables parallel execution of tasks across managed endpoints using various protocols. It supports operations such as data collection, asset discovery, credential rotation, and automated endpoint management at scale.
-
Network Interfaces and Protocol Proxies. The server listens for incoming connections on multiple ports, including:
- HTTPS for web management, Web Sessions, and REST API access
- RDP, SSH, and PowerShell proxies for secure connections initiated by native desktop or mobile clients
Endpoints¶
-
Managed Systems and Access Protocols. 12Port supports a wide range of endpoints, including Windows, Linux, Unix, IBM i servers, network devices, and web portals. These systems can be accessed using protocols such as RDP, SSH, VNC, Telnet, PowerShell/WinRM, and HTTP. This enables users to establish secure, high-trust sessions through either web-based interfaces or native third-party clients.
-
Automation, Discovery, and Credential Management. In addition to interactive access, endpoints such as servers, network devices, and user directories can be managed programmatically. Supported protocols include SSH, VNC, Telnet, PowerShell/WinRM, LDAP, and HTTP REST APIs. These capabilities enable automated credential rotation, asset discovery, and environment segmentation.
-
Deployment Environments. Endpoints can be deployed across diverse environments, including on-premises data centers and cloud platforms. This includes physical hardware as well as virtual machines managed by hypervisors such as VMware, Hyper-V, and Proxmox, as well as infrastructure hosted in AWS, Microsoft Azure, and Google Cloud.